Viruses can sometimes have really weird names. You have keyloggers, DNS poisoners, and spyware. Out of all of them, however, the Trojan horse perhaps has the weirdest name. Viruses typically have a name that clearly describe what they do, but Trojan horses doesn’t really say anything. It’s not even a real horse!
To understand why Trojan horses are called that, we need to go on a history lesson. There was a war called the Trojan War, that took place during 1260–1180 BC. It was a war where the Greeks were trying to take out the city of Troy.
The problem is, Troy had strong defenses, and the Greek army couldn’t get in. However, the Greeks had a plan.
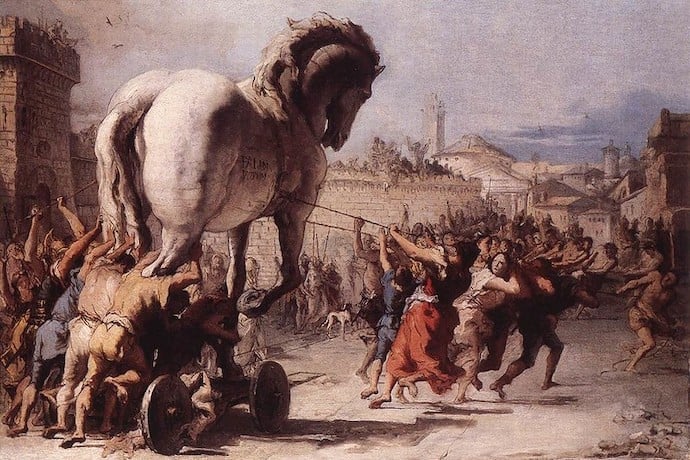
As the story goes, the Greeks built a giant wooden horse on wheels and put 30-50 of their soldiers into the horse, hidden away. The Greeks then wheeled the horse to the front door of Troy and left it there, pretending it was a gift.
The people of Troy, rather pleased with their brand new wooden horse, wheeled it into their city through their guarded gates. Then, during the night, the Greek soldiers crept out of the horse and opened the gates from the inside, allowing the Greek army to siege and take over Troy.
In this story, the city of Troy thought they were receiving a gift when they brought the horse in. Unfortunately, it ended up being a trap, as the nice gesture was actually a way to sneak in soldiers past the city’s defenses.
This horse is known as the Trojan horse, and viruses that work in a similar way to it are called the same thing. Of course, hackers won’t put a wooden horse in front of people’s houses! They instead choose to make their “Trojan horse” more digital.
A Trojan horse virus is when a virus is hidden away in a program that is advertised as good. This is like the Greeks hiding in the Trojan horse, except it’s a virus in a program.
For instance, someone creating a Trojan horse virus may make an alarm app for a phone. The app works perfectly fine, and it does wake you up in the morning, but hidden within it is a virus that deals damage to your phone.
Sometimes a Trojan horse works more like the historical version than you may first think. Trojan horse viruses can establish a connection from the victim’s computer to the hacker’s, much like how the Trojan horse soldiers opened the gates for the main army.
Either way, it’s a good idea to install a good antivirus and keep it updated. These are trained to not be tricked by the digital version of a wooden horse on wheels, so they’re a great way to stay safe from this tricksy threat!
Learn More
Trojan Horse (Historical)
https://www.britannica.com/topic/Trojan-horse
Trojan Horse (Virus)
https://us.norton.com/internetsecurity-malware-what-is-a-trojan.html
What is a Trojan Virus?
https://www.webroot.com/gb/en/resources/tips-articles/what-is-trojan-virus
What is the Trojan Horse Virus?
https://enterprise.comodo.com/what-is-the-trojan-horse-virus.php
How does a Trojan Horse work?
https://www.youtube.com/watch?v=pzOM8sc2RPU
What is a Trojan Horse?
https://softwarelab.org/what-is-a-trojan-horse/
Is the Trojan Horse real?
https://www.discovery.com/exploration/City-Of-Troy-Was-Real
Trojan Horse story for kids
https://greece.mrdonn.org/trojanwar.html
Trojan Horse
https://academickids.com/encyclopedia/index.php/Trojan_horse_%28computing%29
Understanding Trojan viruses
https://www.mcafee.com/blogs/consumer/understanding-trojan-viruses-and-how-to-get-rid-of-them/